IP2: Definition, Functions, Technologies & Modern Use Cases
IP2 is a technical signifier used in network systems to label an “Internet Protocol Layer Point 2,” a classification that identifies a second-level reference within an IP-driven environment. Engineers use IP2 as a functional tag to mark routing points, traffic segments, verification nodes, or metadata layers inside digital communication pipelines.
The term appears in cybersecurity frameworks, geolocation engines, proxy screenings, and device-level intelligence systems. IP2 works as a neutral identifier for systems that process IP-based records, IP-based behavior, or IP-based authentication tasks.
See More: vRealize Infrastructure Navigator (VIN): Complete Technical and Strategic Guide
Core Purpose of IP2
Why IP2 Exists in Network Architecture
IP2 provides a stable labeling structure in frameworks that manage large volumes of IP metadata. It helps servers classify:
-
Routing categories
-
Data checkpoints
-
Verification stages
-
Behavioral snapshots
-
Policy zones
Engineers use IP2 to maintain ordered execution across traffic inspection systems, geolocation engines, and identity-resolution platforms.
How IP2 Works
1. Data Extraction Layer
IP2 captures raw IP attributes from traffic streams. These attributes may include:
-
ASN (Autonomous System Number)
-
ISP identifiers
-
Connection types
-
Address ranges
-
Protocol details
The IP2 layer condenses these variables for later checks.
2. Verification Layer
IP2 verifies the extracted IP information against structured rule sets.
Rule sets can include:
-
Allow lists
-
Block lists
-
Location policies
-
Device signatures
-
Proxy detection rules
3. Output Layer
IP2 outputs standardized data packets.
These packets support:
-
Security engines
-
Fraud-scoring systems
-
Content delivery networks
-
Access-control managers
-
Compliance dashboards
Key IP2 Features
1. Routing Identification
IP2 identifies how traffic flows across networks. It supports load balancing and routing maps used by telecom carriers.
2. Security Enhancement
IP2 supports threat scoring. It detects risky patterns like:
-
Suspicious IP clusters
-
Traffic anomalies
-
High-risk networks
-
Unusual device types
3. Geolocation Interpretation
IP2 can act as an internal tag inside geolocation systems. It organizes IP-based geographic readings with stable context.
4. Proxy Intelligence
IP2 helps systems separate:
-
Clean IPs
-
VPN-based IPs
-
Data-center IPs
-
Residential IPs
-
Tor-exit nodes
-
High-risk proxies
5. Identity Layering
IP2 attaches context to users or devices.
It labels identity-related metadata for fraud prevention or account stability systems.
Modern Use Cases of IP2
1. Cybersecurity Systems
Security suites use IP2 tags to score IP reputations.
IP2-tagged metadata strengthens decisions for:
-
Bot detection
-
Firewall filtering
-
Application protection
-
Credential protection
2. Digital Marketing Analytics
Marketers use IP2 segments to track:
-
Audience zones
-
Connection clusters
-
Network quality indicators
-
Market-level geodata
This helps create precise targeting.
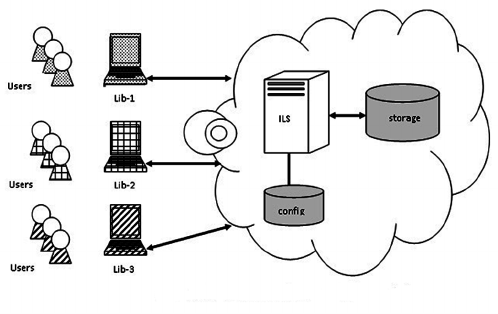
3. Telecom & ISP Management
ISPs use IP2 to map customer traffic.
It improves:
-
Routing accuracy
-
Troubleshooting
-
Network planning
-
Infrastructure monitoring
4. Fraud Prevention Platforms
IP2 supports signals used in:
-
Payment security
-
Account creation checks
-
Session risk analysis
-
Multi-factor validation
5. Streaming & Media Delivery
Content platforms use IP2 labels to manage:
-
Regional licensing
-
Delivery speeds
-
Congestion patterns
-
Device-class distribution
Technical Components Behind IP2
The IP2 classification works with core digital components such as:
1. Address Blocks
IP2 interacts with IPv4 and IPv6 ranges to structure routing information.
2. Network Protocols
It is compatible with:
-
TCP
-
UDP
-
HTTP/2
-
HTTPS
-
QUIC
3. Lookup Tables
IP2 systems store cached data for:
-
ASN lookups
-
ISP flags
-
Country codes
-
Proxy signatures
-
Risk signals
4. Log Pipelines
IP2 information passes through:
-
SIEM logs
-
Server logs
-
Edge logs
-
Authentication logs
This builds a full identity chain.
IP2 Benefits for Organizations
1. Improved Accuracy
IP2 structures IP information in small, accurate units.
This reduces errors in detection systems.
2. Faster Processing
IP2 condenses data, enabling faster security checks.
3. Stronger Compliance
Organizations maintain better IP tracking for privacy and compliance audits.
4. Better Traffic Visibility
IP2 builds clear maps of how users interact with networks.
5. Reduced Fraud
IP2 provides signals that identify bad actors earlier in the session.
Challenges Linked to IP2
1. Data Freshness
IP data changes quickly.
IP2 systems require rapid updates.
2. Complex Integration
Enterprises need stable pipelines to fully use IP2 classifications.
3. Multi-Layer Conflicts
IP2 can overlap with other metadata tags if not architected well.
4. Rate Limits
Large traffic volumes strain IP2 lookup systems.
Comparison of IP Layer Labels
| Layer Label | Function | Use Case | Data Type |
|---|---|---|---|
| IP1 | Base IP capture | Raw logging | Basic values |
| IP2 | Verified IP metadata | Security, analytics | Structured metadata |
| IP3 | Behavioral enrichment | Fraud insights | High-context data |
Common IP2 Output Attributes
-
Country code
-
Region code
-
City code
-
ISP name
-
ASN value
-
Proxy label
-
Device class
-
Connection type
-
Traffic risk flag
-
Routing density score
IP2 in Emerging Technologies
1. AI-Driven Security Systems
IP2 supports machine learning models with clean, structured IP signals.
2. Zero-Trust Networks
IP2 provides identity-linked data for every access request.
3. Edge Computing
IP2 assists distributed nodes in understanding user location and behavior.
4. Connected IoT Ecosystems
IP2 helps IoT gateways track device clusters with high accuracy.
See More: iOS App Development from Garage2Global: A Complete Guide to High-Performance Mobile Innovation
FAQs About IP2
1. What does IP2 mean in network systems?
IP2 represents a second-level IP classification used to tag verified IP metadata within security, routing, and analytics systems.
2. How is IP2 different from raw IP data?
Raw IP data contains basic numbers. IP2 contains enriched, context-driven information.
3. Where is IP2 used most often?
IP2 appears in cybersecurity platforms, geolocation engines, proxy-detection systems, and digital marketing analytics.
4. Does IP2 involve identity tracking?
IP2 connects IP data with behavioral metadata, which supports identity-resolution tasks in fraud prevention systems.
5. Is IP2 the same as IP geolocation?
No. IP2 can include geolocation data, but it also contains risk, network, protocol, and device-class details.
6. Can IP2 detect proxies?
Yes. IP2 metadata includes proxy labels, Tor-exit indicators, VPN tags, and data-center flags.
7. Why do companies rely on IP2?
IP2 improves accuracy in risk scoring, routing, compliance, analytics, and content delivery.
8. How does IP2 help with fraud prevention?
IP2 identifies unusual network signals that often appear in fraudulent sessions.
9. Does IP2 work with IPv6?
Yes. IP2 supports both IPv4 and IPv6 ranges.
10. Can IP2 support AI systems?
Yes. IP2 offers structured inputs that feed machine learning models.
Conclusion
IP2 acts as a structured metadata layer that transforms raw IP addresses into meaningful network intelligence. It improves routing, strengthens security, supports analytics, and enhances identity-driven decisions across digital ecosystems. Its use spans cybersecurity, telecom, marketing, fraud prevention, and emerging AI systems. As networks evolve, IP2 remains a core component of precise IP classification and responsible digital infrastructure.